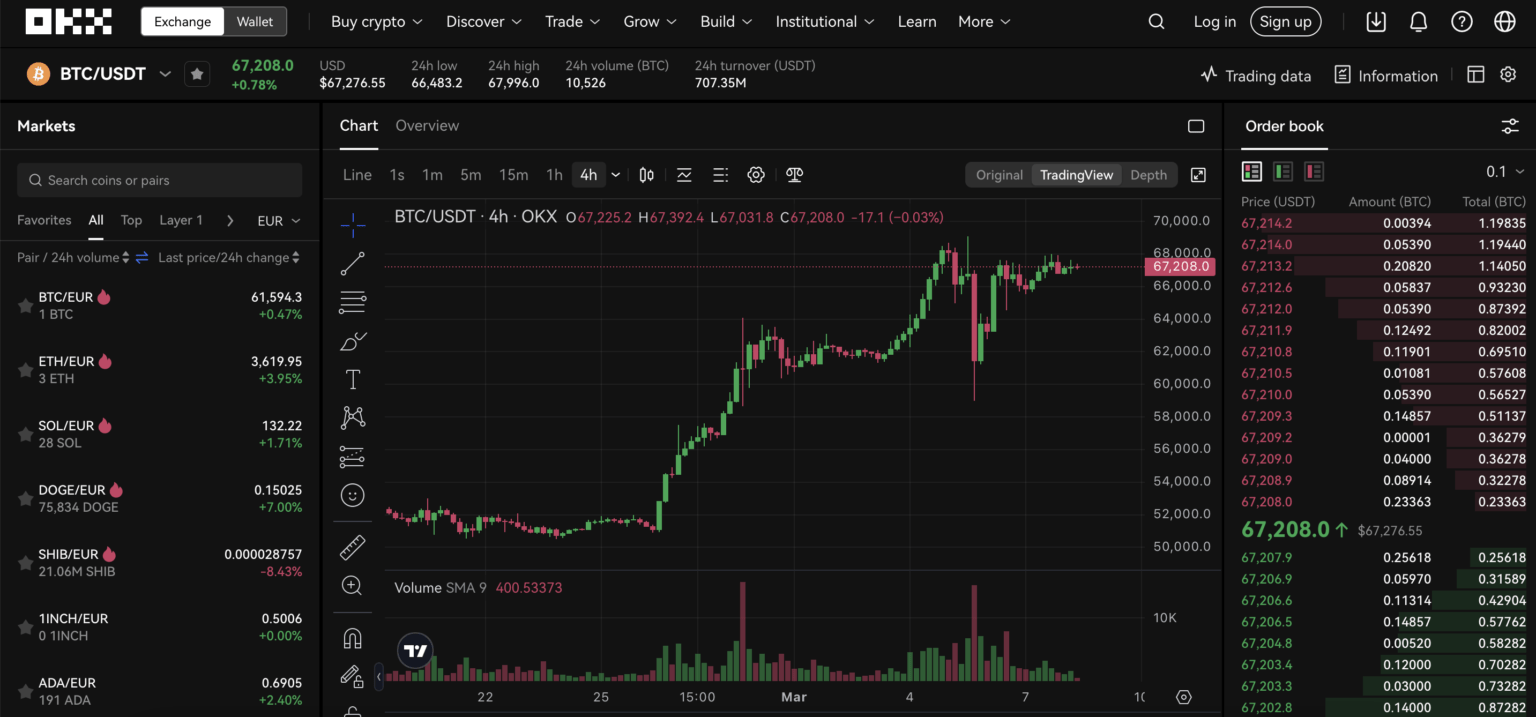
Many traders assume that if they can log in to an exchange and see balances, they have full control and safety. That’s a convenient but dangerous shortcut. With platforms like OKX — which combine centralized exchange services, a Web3 wallet, derivatives, and staking — “being logged in” is just one point on a chain of custody, verification, and operational decisions that determine whether assets are usable, safe, or irrevocably lost.
This article walks through a practical case-led scenario: a mid-sized U.S. retail trader who needs to access OKX to move funds, stake, and trade futures after a temporary travel interruption. We’ll use that scenario to explain how OKX login and verification work in practice, what the important security mechanisms are, where they break down, and how to make day-to-day decisions that reduce real risk. The emphasis is on mechanisms (how login and verification actually function), trade-offs (convenience versus exposure), and limits (what the exchange does and what users must still manage).
Case scenario: Logan, the U.S. trader who needs access
Logan is based in the U.S., trades spot and occasional margin, and uses OKX for staking a portion of his ETH and for a handful of altcoins available there. He left town for a week, carried only his phone, and now needs to log in from a hotel network. He knows his password but paused on whether to use SMS 2FA, Google Authenticator, or biometric login on his phone. He also hasn’t completed KYC for higher withdrawal limits.
This scenario surfaces the core operational questions every U.S. trader should answer before traveling: which authentication paths are available, how the platform enforces identity verification, what happens to withdrawals during suspicious login attempts, and how custody choices (custodial exchange vs self-custodial wallet) change the stakes.
How OKX authentication and verification work — mechanism first
At the entry level, OKX provides a standard web and mobile login flow protected by military‑grade encryption: username/email + password, plus mandatory Two‑Factor Authentication (2FA). The platform supports SMS 2FA, TOTP (e.g., Google Authenticator), and biometric unlock on the mobile app. It also features AI-driven threat-detection that flags suspicious logins and can trigger holdbacks or extra verification steps.
For regulatory compliance and higher-functional access (large withdrawals, derivatives, fiat on/off ramps), OKX requires Know Your Customer (KYC) verification. In the U.S. context that means submitting a government-issued ID and a facial-recognition liveness check. The technical mechanism: the exchange verifies identity documents against the live selfie data using automated checks; policy and thresholds then determine whether to grant full trading and withdrawal rights or to limit the account.
Beyond online authentication, custody matters. OKX is a centralized exchange that stores the majority of funds (over 95%) in cold, air-gapped, multi‑signature storage. That reduces certain hacking vectors but does not remove user-side risks like phishing, account takeover, or the irreversible loss entailed by losing a self-custodial seed phrase if a user chooses to use the OKX Web3 wallet instead of on-exchange custody.
Trade-offs and failure modes: convenience vs control
Here are the practical trade-offs Logan faces and the likely failure modes to watch for:
– SMS 2FA: convenient when traveling, but vulnerable to SIM swap attacks. In the U.S., SIM swaps are a known attack vector; attackers with a successful swap can bypass SMS-based 2FA and request account resets. OKX mitigates this by combining threat detection with manual review for high-risk actions, but the residual risk remains.
– Authenticator apps (TOTP): stronger against SIM attacks, but require prior setup and a backup plan (seed/exported codes). If Logan loses his phone without an exported TOTP backup and the exchange requires it for verification, recovery can be slower and more intrusive.
– Biometrics: quick and effective for local device unlock, but device compromise or coerced access are non‑technical concerns. Biometrics do not replace second‑factor protocols for account recovery — they are a convenience layer bound to a device.
– KYC vs non-KYC: completing identity verification increases withdrawal and product access, but it creates a centralized identity trail. For U.S. users, that is often unavoidable for fiat on/off ramps and derivatives. The trade-off is regulatory compliance and higher limits versus privacy and data-minimization.
Where the system breaks: realistic limitations and gaps
Understanding limits is practical: OKX’s Proof of Reserves provides on-chain transparency that the exchange maintains backing for deposited assets — but PoR does not guarantee individual access during a specific outage, nor does it prevent temporary freezes resulting from suspicious logins or regulatory holds. PoR is a solvency transparency tool, not an access SLA.
Cold storage protects against many online breaches, but withdrawals still require signatures that depend on internal operational controls. That means large-scale withdrawal delays can occur if internal multi-sig signers are offline or if the security team freezes movements during an incident. A user who needs immediate liquidity should not assume instant cold-wallet withdrawals.
When using the OKX Web3 non-custodial wallet, users regain key control but accept new risks: losing seed phrases or exposing them to malware and phishing means permanent loss. The mental model that “self-custody equals perfect safety” is wrong — it trades third‑party custody risks for personal operational risks.
Operational checklist: rules Logan (and you) should apply
From the case and the mechanisms above, a concise rule-set emerges. Each rule is a decision heuristic you can reuse:
1) Pre-travel setup: enable TOTP, export backup codes, confirm biometric unlock works locally, and register a hardware wallet if you use the Web3 wallet. Test a small withdrawal before travel to validate access paths.
2) Threat minimization: prefer authenticator apps over SMS for 2FA; if SMS is unavoidable, notify your mobile provider of travel plans and add a PIN to your carrier account when possible.
3) Identity trade-off: if you need higher limits or derivatives, complete KYC ahead of time. Factor in the time for manual reviews — don’t wait until you need emergency access.
4) Liquidity contingency: keep a small buffer on a custodial platform for quick trade execution, but diversify critical holdings into cold storage and/or a hardware-connected Web3 wallet for long-term holdings.
5) Phishing discipline: always check the URL and use official app stores; consider a browser extension or password manager that autofills only on exact domain matches to reduce spoofed-site risk. For convenience, consider bookmarking the official login and use no-search navigation on travel networks.
Product features that matter for the U.S. trader
Several OKX features are especially relevant to U.S. users and to Logan’s case: the platform supports more than 300 assets and over 130 blockchains, enabling broad access, but that breadth increases the surface area for mistakes (trading unfamiliar altcoins, cross-chain bridges, or new DeFi pools). Futures and derivatives (up to 125x on certain contracts) amplify returns and risks — for U.S. traders, leverage products often come with added verification and compliance controls.
Staking and yield options (flexible, fixed lock-ups, DeFi farming, auto-compounding) can earn passive income but introduce lock-up and liquidity timing risks. If Logan stakes ETH in a locked pool and then loses account access, the staked funds may be illiquid for the lock-up period. Similarly, interacting with the OKX DEX aggregator and cross-chain bridges can expose users to smart-contract risk; these are technical risks separate from the exchange’s custodial protections.
Decision-useful heuristics and a final mental model
Two portable heuristics emerge: (1) Treat “login success” as necessary but not sufficient for asset access. Test the full withdrawal and recovery path before you need it. (2) Map custody to function: use custodial exchange balances for trading liquidity, a hardware or self-custodial wallet for long-term storage, and a small hot balance for operational needs.
Conceptually, think of your relationship with OKX as layered permissions. Authentication gets you into the UI. 2FA and device attestations gate sensitive actions. KYC and internal risk scoring gate higher withdrawal and product access. Cold-storage operations are the final step that moves an asset materially. Break any one link and access can be delayed or blocked; hardening each link reduces systemic risk.
What to watch next — conditional signals, not predictions
Monitor three signals that change the operating picture: (1) regulatory guidance in the U.S. affecting KYC thresholds or derivatives access — tighter rules will increase verification friction and potentially delay account actions; (2) exchange delistings and liquidity moves — the recent delisting of niche pairs is an example of routine maintenance that can change market liquidity for specific assets; (3) security incident trends — large exchange incidents change how custodial insurance and user verification are handled.
These are conditional scenarios: if regulatory pressure increases, expect longer review times and stricter identity checks; if market delistings expand, some altcoins will move to lower‑liquidity venues, increasing slippage and exit costs; if large breaches occur elsewhere, exchanges may tighten withdrawal policies temporarily. None of this is predestined — each is an outcome to watch and respond to.
FAQ
How should I choose between SMS, authenticator app, and biometrics for OKX login?
Prefer an authenticator app (TOTP) for everyday 2FA because it resists SIM-swap attacks. Use biometrics for local convenience on your phone, and avoid SMS for primary 2FA if you can. If you must rely on SMS while traveling, add carrier protections and ensure alternative recovery options are set up.
Will completing OKX KYC reduce my security?
KYC trades some privacy for increased access and regulatory compliance. It does not inherently reduce cryptographic protections, but it creates a centralized identity record. Consider whether you need higher withdrawal or derivatives limits; if not, you can maintain a lower profile with limited KYC while recognizing product restrictions.
What happens if I lose access to my authenticator or phone?
Recovery typically requires account verification steps that can include identity documents and liveness checks. That process can take days and may be slower under high-risk flags. The permanent-loss risk is higher for self-custodial seed phrases — exchanges can (sometimes) help with account recovery, while lost private keys are unrecoverable.
Should I use the OKX Web3 wallet or leave everything on the exchange?
Use both according to function: keep active trading funds on the exchange for liquidity and low-friction execution; use the Web3 wallet with hardware integration for long-term holdings and direct DApp interactions. Understand that self-custody shifts operational responsibility (seed safety, secure backups) onto you.
Where can I find the official OKX login page and more setup guidance?
For step-by-step directions to access the web login and platform entry points, use the official resource: okx login. Always verify the URL before entering credentials and prefer direct bookmarks to search results.